-
Gallery of Images:

-
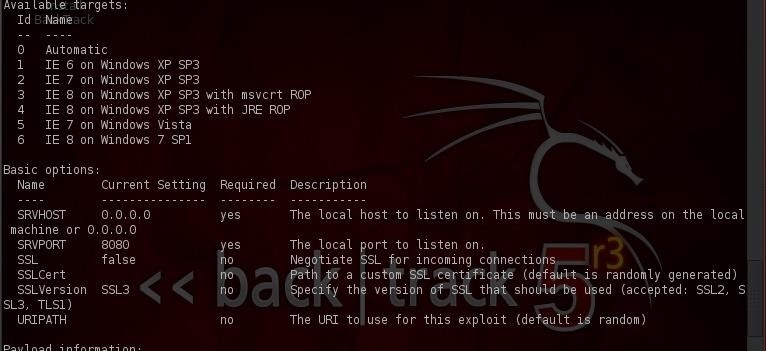
How To Exploit Windows 8 With Metasploit In this article were going to learn how to exploit (Windows 8 Preview Build 8400) with clientside attack technique, well get. Browserautopwn may not work on your chosen target's web browser Target in the video is running Windows XP SP2 Windows XP SP2 ( First target ) has a firewall and it's enabled, however, as the attack is reversed and the target connects back to the attacker which allows the connection happen. Hi everyone, Today, I'd like to debut a completely rewritten new cool toy for Metasploit: Browser Autopwn 2. Browser Autopwn is the easiest and quickest way to explicitly test browser vulnerabilities without having the user to painfully learn everything there is about each exploit and the remote target before deployment. On 11: 00 PM, firstname lastname wrote: I am trying to gain Local System Privileges on a Windows 7 x86 target system. I have a meterpreter reverse tcp shell on the victim's machine after a successful browser exploit on MSIE version 8. 0 running on the target machine. Using metasploit its possible to hack windows xp machines just by using the ip address of the victim machine. It does not involve installing any backdoor or trojan server on the victim machine. Metasploit does this by exploiting a vulnerability in windows samba service called ms0867. Hack Windows 7 with Metasploit using Kali Linux Today i am gonna show how to exploit any windows OS using metasploit. Exploiting a windows vulnerability to logging into the system with out username and password using Metasploit. Here's I got from metasploit about this exploit: This module exploits a vulnerability found in Microsoft Internet Explorer. A useafterfree condition occurs when a CDwnBindInfo object is freed by FollowHyperlink2, but a reference is kept in CDoc. Hack Windows 7 with Metasploit using Kali Linux LINUX DIGEST LINUX DIGEST A Linux Engineer and Security Researcher Blog In this video we have used browser Autopwn vulnerability to from Metasploit Framework to hack windows 7. 1st go to metasploit and search foe brwoserautopwn Metasploit has contributed to the Exploit Database with remote exploits, local vulnerabilities, web applications, shellcode, papers and Google Hacking Database This module exploits a buffer overflow in Apple QuickTime. This module was inspired by MOAB. The Browser target for this module was tested against IE 6 and Firefox. 3 on Windows XP SP02; Firefox 3 blacklists the QuickTime plugin. The Windows XP target has to have QuickTime installed for this module to work. It uses a ROP chain from a non safeSEH enabled DLL to bypass DEP and safeSEH. The stack cookie check is bypassed by triggering a SEH exception. How To Exploit Hack Windows 8 With Metasploit Allot of you want to Hack Windows 8 In this article were going to learn how to exploit (Windows 8 Preview Build 8400) with clientside attack technique, well get meterpreter session on windows 8 machine. Machine 2: Target Windows 7 Machine Msfconsole is by far the most popular part of the Metasploit Framework, and for good reason. It is one of the most flexible, featurerich, and well Amigos esta vez les quiero compartir una de las actividades practicas que he realizado con mis alumnos de Taller de Seguridad en Redes y se trata de como hackear un sistema operativo Windows 7 con Kali linux y metasploit en pocos pasos. Back to search MS Microsoft Internet Explorer execCommand UseAfterFree Vulnerability. This module exploits a vulnerability found in Microsoft Internet Explorer (MSIE). Ahora, vamos a ir a nuestro equipo con Windows 7 y escriba la direccin URL de nuestro servidor web malicioso que hemos construido en Metasploit Mientras que estamos haciendo eso, podemos ver en Metasploit que las cosas se estn agitando. El siguiente video muestra como utilizar Armitage para ejecutar cdigo arbitrario en un sistema Windows 7. Esta es la descripcin del mdulo utilizado para el exploit. The target machine is Windows7 and target application is IE8. I am using exploits such as ms, ms for which 'IE8, W7 target' is compatible. IE8 crashes when exploited using metasploit framework. Come molti di voi sanno gi, lexploit un segmento di codice che, sfruttando un bug o una vulnerabilit, porta allacquisizione di privilegi o al denial of service di un sistema. Per acquisire il controllo della macchina Windows 7 abbiamo bisogno anche noi di generare un exploit e iniettarlo nella macchina ospite. metasploitpayloads, mettle These are Metasploit's payload repositories, where the wellknown Meterpreter payload resides. Meterpreter has many different implementations, targeting Windows, PHP, Python, Java, and Android. This is the ocial user guide for version 3. 2 Installation on Windows The Metasploit Framework is fully supported on the Windows platform. To oer a process and le browser via the rightclick context menu. 3 The Command Line Interface Metasploit is a penetration testing platform that enables you to find, exploit, and validate vulnerabilities. The platform includes the Metasploit Framework and its commercial counterparts: Metasploit Pro, Express, Community, and Nexpose Ultimate. How to Hack Windows 7 in LAN using Metaspolit (Metasploit Browser Autopwn) The Metasploit Framework provides different mixins you can use to develop a browser exploit, mainly they are: The BrowserExploitServer mixin is the only mixin specially designed for browser exploitation. Before you use this mixin, you should understand what it does behind the scenes for you: It. Metasploit Pro is an exploitation and vulnerability validation tool that helps you divide the penetration testing workflow into smaller and more manageable tasks. With Metasploit Pro, you can leverage the power of the Metasploit Framework and its exploit database through a web based user interface t The Metasploit Project is an opensource, computer security project which provides information about security vulnerabilities and aids in penetration testing and IDS signature development. Its most wellknown subproject is the Metasploit Framework, a tool for developing and executing exploit code against a remote target machine. We have some Metasploit freshness for you today: A new zeroday exploit for Internet Explorer 7, 8, and 9 on Windows XP, Vista and 7. Computers can get compromised simply by visiting a malicious website, which gives the attacker the same privileges as the current user. Windows Browser Example Exploit Posted Jul 15, 2017 Authored by sinn3r Site metasploit. This template covers IE8910, and uses the useragent HTTP header to detect the browser version. El MS es el modulo (exploit) incluido en metasploit que explota un problema de desbordamiento (heap overflow) en la libreria winmm. dll (libreria de multimedios de windows). com Available targets: Id Name SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC) Payload information: Space: 370 The default target for this exploit should succeed on Windows NT. In this tutorial, we will exploit Internet Explorer CSS recursive call memory corrruption vulnerability in Internet Explorer 8 in Windows 7 Service Pack 1 (unpatched) using Metasploit in Kali Linux and get a remote shell on the Windows 7 machine. The Metasploit browser exploit method will utilize select Metasploit browser exploits through an iframe and deliver a Metasploit payload. The Credential Harvester Method will utilize web cloning of a website that has a username and password field and harvest all. 110 is the IP address of Instructor (metasploit machine). Command: set URIPATH auroraexploit. html This will be the name of the webpage file the misinformed user with Windows Exploder 6 will click on. Once the browser tries to load the page, you will see a msf message saying 'Sending Internet Explorer Aurora Memory Corruption to client. ' Back to the WindowsVulnerable VM After your Windows Exploder tries to load the web page it will become unstable, crash, and you will see the below Microsoft Message. UPDATE ( ): The original article was written in 2011 and pretty much outdated, I've updated the numbers and conclusions. I've got a question about which programming language is preferable for the website development for embedded systems (with limited resources). Lets HACK into Windows 7 Hacking Tool: Metasploit Project is a computer security project that provides information about security vulnerabilities. Por otro lado, para acceder a cualquier Sistema Windows 7 o XP nos basaremos en la ultima vulnerabilidad 0day que se registro en el Navegador Internet Explorer versiones 7 8 y 9 la cual permite que cualquier 'atacante' puede utilizar el exploit respectivo para tomar acceso completo al. 03 Metasploit Basics Attacking the Browser Leave a comment Go to comments When first learning about offense, students are often bewildered by the variety of different attacks that exist against a system, and often begin to believe that any system is vulnerable to anything. Por otro lado, para acceder a cualquier Sistema Windows 7 o XP nos basaremos en la ultima vulnerabilidad 0day que se registro en el Navegador Internet Explorer versiones 7 8 y 9 la cual permite que cualquier 'atacante' puede utilizar el exploit respectivo para tomar acceso completo al. En este entrada se describir como explotar un Sistema Windows, ya sea XP o 7, mediante la vulnerabilidad MS Microsoft XML Core Services MSXML Uninitialized Memory Corruption desde el Metasploit de una forma rpida y divertida como acostumbramos a hacerlo. Windows XP and earlier Windows version (I use Windows 7 SP1) Step by Step: FYI in this tutorial I use Backtrack 5 R2 with Metasploit Framework, and my IP address is. Contribute to development by creating an account on GitHub. I was playing around with metasploit and I thought it was pretty cool. There was a Java Rhino Exploit which allows you to gain control of a windows machine. I wanted to give it a shot and see what kind of bad things we can do: ) To demonstrate the exploit I had two VMs in my VMware Fusion running, Windows 7. Metasploit Community is a professional software application specialized in offering information about security vulnerabilities with the aid of penetration testing. The worlds most used penetration testing framework Knowledge is power, especially when its shared. A collaboration between the open source community and Rapid7, Metasploit helps security teams do more than just verify vulnerabilities, manage security assessments, and improve security awareness; it empowers and arms defenders to always stay one step (or two) ahead of the game. Using Kali Linux v2, I walk you through how to run a module of Metasploit called Browser Autopwn. This simulates what would happen to you if you use an outdated browser and click the wrong link on. Today i am gonna show how to exploit any windows OS using metasploit. Exploiting a windows vulnerability to logging into the system with out username and password using Metasploit. In the worst case, all of the exploits running against the browser can crash the browser. Although autopwn is a good Metasploit training tool, it is less than stealthy and often will overwhelm the browser with exploits and crash it. Step 3: Add New Module to Metasploit. Earlier this year, I wrote a tutorial on how to install a new module in Metasploit, so please refer to that if you need more help on this subject. You will need to add this module to your Metasploit framework before we can proceed..
-
Related Images: